
The traditional security perimeter is gone. With workforces distributed across continents, applications running in multi-cloud environments, and threat actors operating with nation-state sophistication, the castle-and-moat model of enterprise security has become a liability. Zero Trust Architecture is no longer a forward-looking aspiration. It is the baseline for any organization serious about protecting its data, its people, and its operations.
This guide provides a practical, implementation-focused roadmap for enterprise security teams adopting Zero Trust principles in 2025 and beyond. Whether you are migrating from a legacy VPN-centric model or hardening an existing identity-aware infrastructure, the frameworks and pitfalls outlined here are drawn from real-world deployments across regulated industries.
Why Perimeter-Based Security Is Obsolete
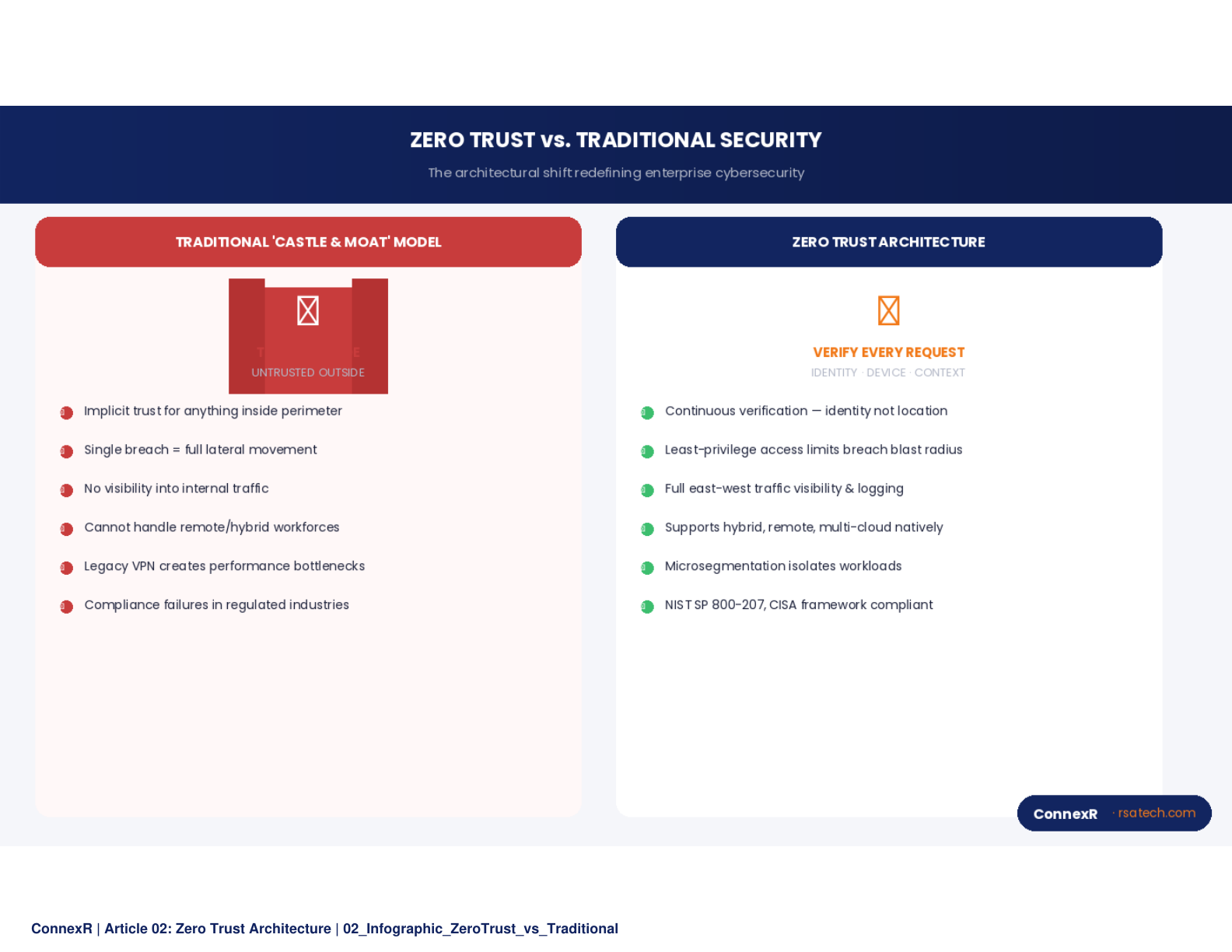
For decades, enterprise security operated on a simple assumption: everything inside the network perimeter is trusted, and everything outside is not. Firewalls, VPNs, and DMZs were the primary tools. This model worked when employees sat in offices, applications lived in on-premises data centers, and the attack surface was relatively contained.
That world no longer exists. Cloud-native architectures distribute workloads across AWS, Azure, and GCP simultaneously. SaaS applications mean corporate data flows through dozens of third-party platforms. Remote and hybrid workforces connect from personal devices on home networks. The perimeter, in any meaningful sense, has dissolved.
"The breach that matters is not the one that penetrates your firewall. It is the one that moves laterally for 200 days because you trusted everything inside your network by default."
The statistics reinforce this shift. According to industry research, over 80 percent of breaches now involve compromised credentials or insider access, not external network penetration. Attackers do not need to break through the perimeter when they can simply log in with stolen credentials and exploit implicit trust within the network.
Core Zero Trust Principles
Zero Trust is not a product you purchase. It is an architectural philosophy built on three foundational principles that must permeate every layer of your security posture.
Never Trust, Always Verify. Every access request is treated as if it originates from an untrusted network, regardless of where the user or device is located. Authentication and authorization are enforced continuously, not just at the point of entry.
Least-Privilege Access. Users, services, and applications receive the minimum permissions necessary to perform their function. Access is scoped by role, context, and time. Standing privileges are eliminated wherever possible in favor of just-in-time access grants.
Assume Breach. Design your architecture as though an attacker already has access to your environment. Segment networks aggressively, encrypt data in transit and at rest, and ensure that a compromise in one zone cannot cascade across the enterprise.
The Five Implementation Pillars
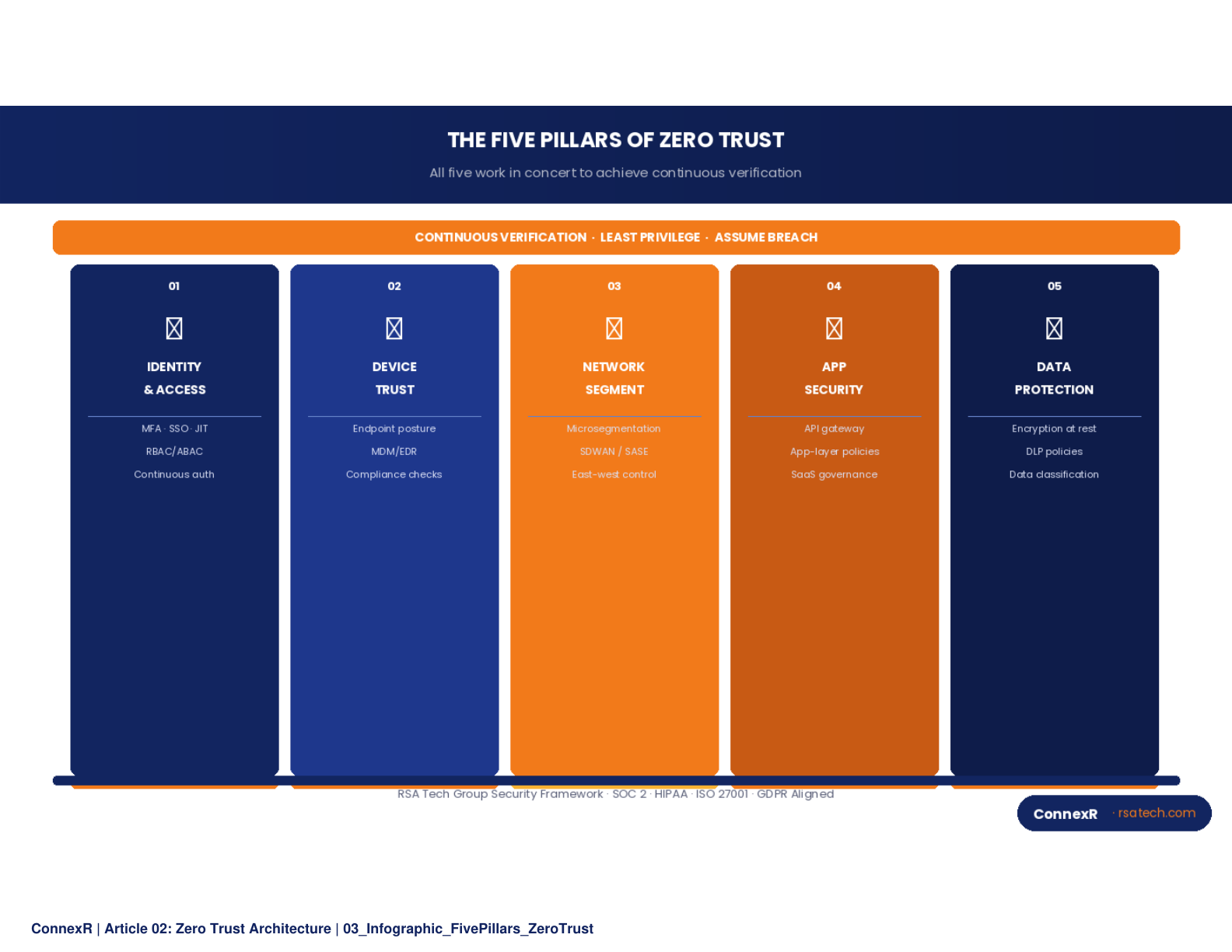
A comprehensive Zero Trust deployment addresses five interdependent pillars. Neglecting any one of them creates gaps that sophisticated attackers will exploit.
1. Identity
Identity is the new perimeter. Every access decision begins with strong identity verification. This means deploying multi-factor authentication universally, not just for VPN access or privileged accounts. It means implementing conditional access policies that evaluate risk signals such as device health, location anomalies, and behavioral patterns before granting access. Federated identity management through standards like SAML 2.0 and OpenID Connect ensures consistency across cloud and on-premises environments. Passwordless authentication using FIDO2 keys or biometrics reduces the single largest attack vector in most organizations.
2. Device
A verified identity on a compromised device is still a threat. Zero Trust requires continuous device health assessment: is the endpoint running current patches, does it have endpoint detection and response (EDR) active, is its disk encrypted, does it comply with the organization's security baseline? Device trust must be evaluated at the moment of access and re-evaluated throughout the session. Mobile device management and endpoint compliance engines feed real-time signals into access policy decisions.

3. Network
Flat networks are a Zero Trust anti-pattern. Micro-segmentation divides the network into isolated zones so that lateral movement becomes difficult even after initial compromise. Software-defined perimeters replace traditional VPNs, providing application-level access without exposing the broader network. East-west traffic inspection, long neglected in favor of north-south perimeter controls, becomes essential. DNS-layer security adds another enforcement point that operates before a connection is even established.
4. Application
Applications must authenticate and authorize every request, not just the initial session. API gateways enforce rate limiting, schema validation, and token verification at the edge. Runtime application self-protection (RASP) detects exploitation attempts from within the application itself. Container and serverless workloads require service mesh architectures that enforce mutual TLS between microservices, ensuring that even internal service-to-service communication is encrypted and authenticated.
5. Data
Data is what attackers ultimately want. Classification and labeling ensure that sensitive data is identified and governed appropriately. Data loss prevention (DLP) policies enforce controls at the point of egress, whether that is an email attachment, a cloud storage download, or an API response. Encryption must be applied at rest, in transit, and increasingly in use through technologies like confidential computing. Access to data should be governed by attribute-based policies that consider who is requesting it, from what device, in what context, and for what purpose.
Step-by-Step Implementation Roadmap
Zero Trust is a multi-year transformation, not a single project. The following phased approach has proven effective in enterprise environments with complex legacy footprints.
"The organizations that succeed with Zero Trust are the ones that treat it as a continuous program, not a one-time migration. Start with identity, demonstrate value quickly, and expand methodically."
Phase 1: Assessment and Identity Foundation (Months 1 to 3). Conduct a comprehensive audit of your current security architecture. Map all users, devices, applications, and data flows. Deploy universal MFA and conditional access policies. Establish an identity governance framework. This phase delivers immediate risk reduction and builds organizational confidence in the program.
Phase 2: Device Trust and Network Segmentation (Months 4 to 8). Roll out endpoint compliance requirements. Implement device health checks as access policy inputs. Begin micro-segmentation starting with your most sensitive workloads. Replace legacy VPN access with software-defined perimeter solutions for critical applications.
Phase 3: Application and Data Controls (Months 9 to 14). Enforce application-level authentication for all internal services. Deploy API gateways with Zero Trust policies. Implement data classification and DLP controls. Establish encryption standards for data at rest and in transit across all environments.
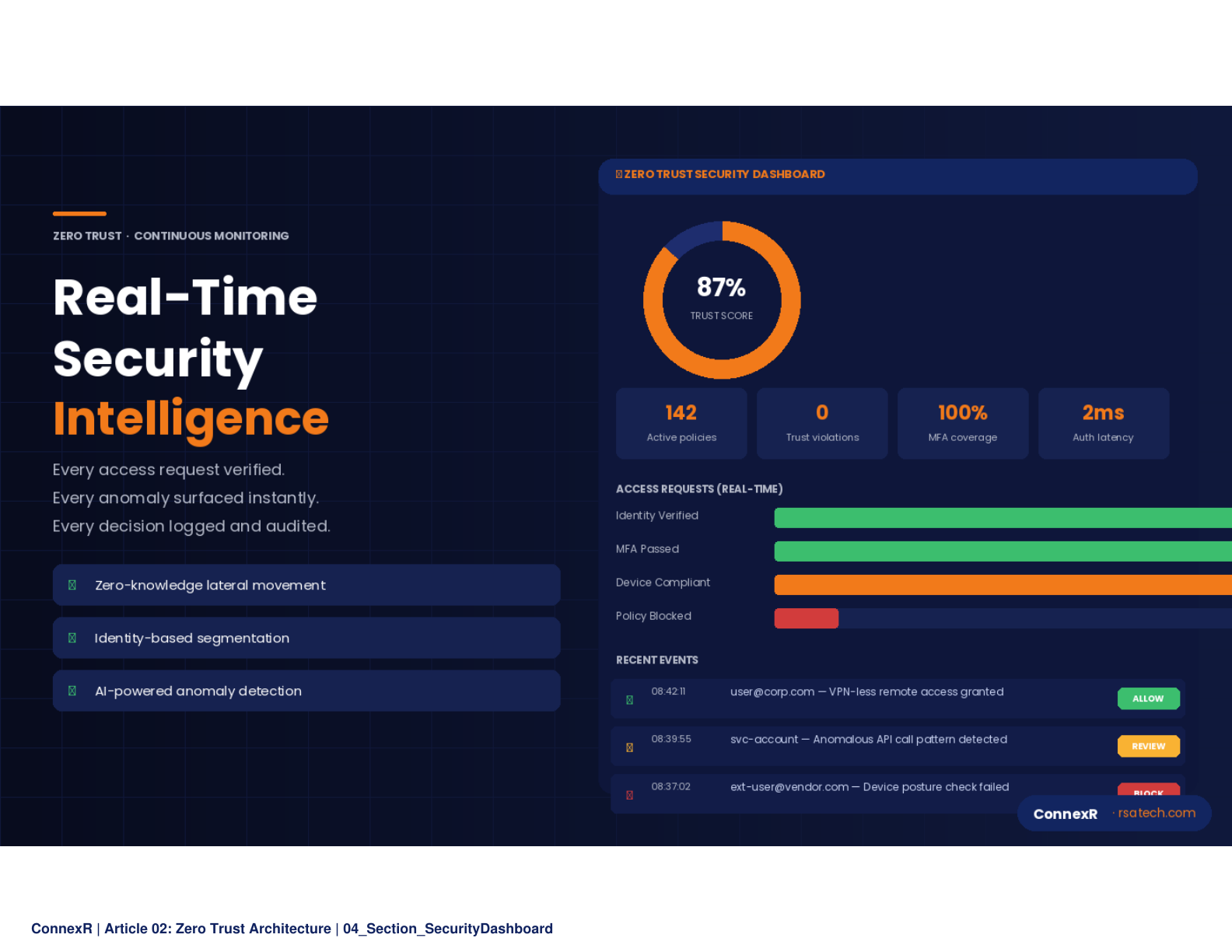
Phase 4: Continuous Monitoring and Automation (Months 15 to 18 and ongoing). Integrate all telemetry into a unified security operations platform. Deploy automated response playbooks for common threat scenarios. Implement continuous access evaluation that can revoke sessions in real time when risk signals change. Conduct regular red team exercises to validate the architecture under adversarial conditions.
Common Pitfalls and How to Avoid Them
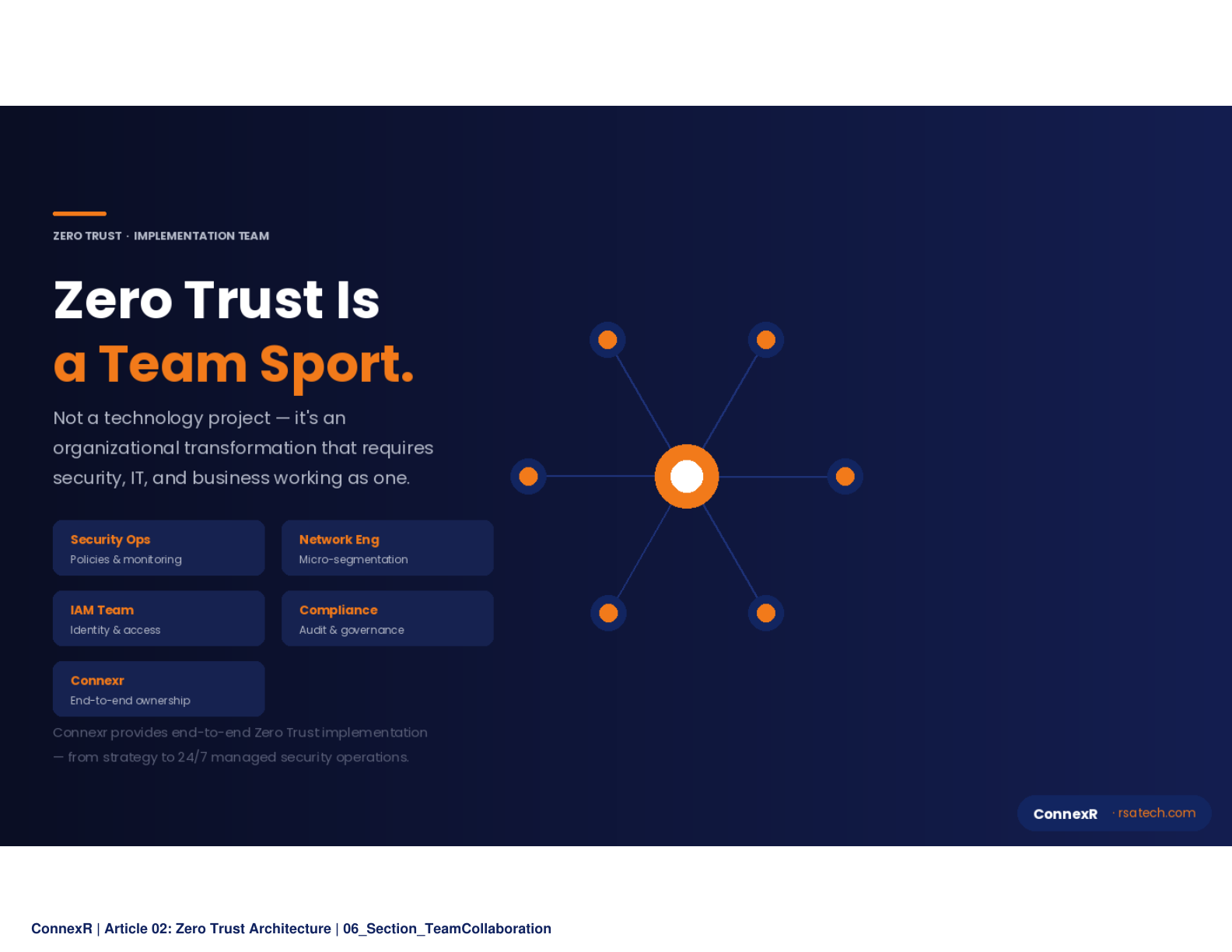
The most common failure mode in Zero Trust adoption is not technical. It is organizational. Teams attempt to implement everything at once, create excessive friction for end users, and lose executive sponsorship when productivity complaints mount. A phased approach with clear metrics at each stage prevents this.
Another frequent mistake is treating Zero Trust as a vendor purchase rather than an architectural transformation. No single product delivers Zero Trust. It requires orchestration across identity providers, endpoint management platforms, network infrastructure, and application security tools. Organizations that buy a "Zero Trust product" and declare victory find themselves with expensive shelfware and unchanged risk posture.
Neglecting the user experience is equally dangerous. If Zero Trust controls make it harder for employees to do their jobs, they will find workarounds that create new security gaps. The best implementations are invisible to end users: single sign-on reduces authentication friction, conditional access applies step-up verification only when risk signals warrant it, and automated device compliance checks run silently in the background.
Finally, many organizations underestimate the importance of data classification. Without understanding what data you have, where it lives, and who accesses it, you cannot build effective policies. Data discovery and classification should be among the first workstreams, not an afterthought.
Integration with Existing Security Tools
Zero Trust does not require ripping out your existing security stack. It requires making that stack work together with identity as the common thread. Your SIEM (Security Information and Event Management) platform becomes the central nervous system, correlating signals from identity providers, endpoints, network devices, and applications to detect anomalous patterns that no single tool could identify alone.
SOAR (Security Orchestration, Automation, and Response) platforms automate the response to common threats, reducing mean time to containment from hours to seconds. When a compromised credential is detected, automated playbooks can revoke sessions, quarantine the affected device, trigger a password reset, and open an incident ticket without human intervention.
IAM (Identity and Access Management) serves as the policy engine. By centralizing access decisions in a modern IAM platform that supports attribute-based access control (ABAC), you ensure consistent enforcement regardless of whether the user is accessing a cloud SaaS application, an on-premises legacy system, or an API endpoint. The integration between IAM and your SIEM creates a feedback loop: access patterns inform risk scoring, which in turn adjusts access policies dynamically.
Zero Trust is a journey, not a destination. The organizations that start now will be the ones best positioned to weather the next generation of threats.
ConnexR helps enterprises design, implement, and operationalize Zero Trust Architecture across hybrid and multi-cloud environments. Our team brings deep expertise in identity, network security, and compliance for regulated industries.
— Security Operations | ConnexR